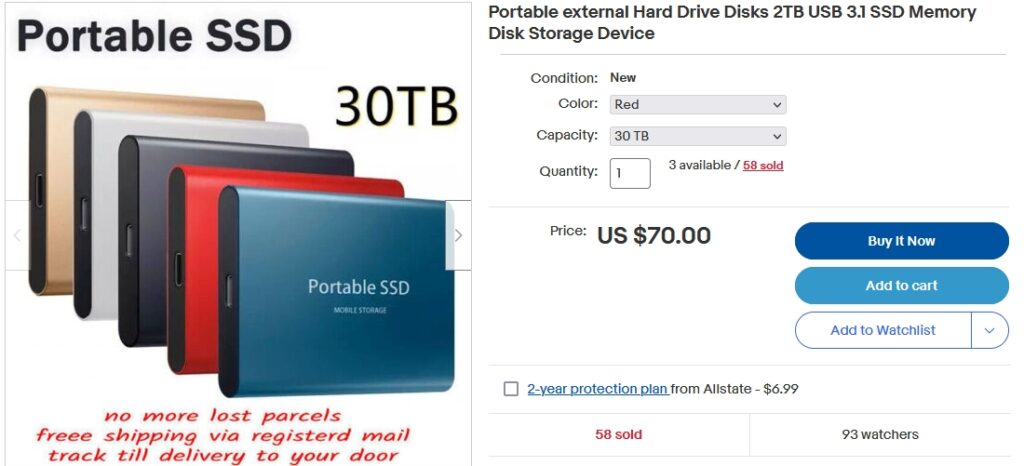
That’s not news; it was always true that you can find fake Rolexes in the worst parts of some cities. But now it’s the Piranha Plant from the Mario Brothers games, as an insect-eating plant you can grow from seeds available on Amazon. (Nope. They’re weed seeds.) And there’s a 30Terabye solid state drive, portable model, for $70. If that was real, it would cost well into the 4 figures, but no, it’s only $70, because it’s 60 Gb of micro SD card and a trick BIOS that reports a very large drive that doesn’t exist and let’s you copy unlimited files to nowhere.
Here’s how to recognize these frauds, and others that are more subtle. It’s in the December 2022 PC Updater News, available free here. (Plus back issues and a free subscription.)

